OVERKILL
$100 Site Donor 2021
VPN firm that claims zero logs policy leaks 20 million user logs
Follow us on Twitter @HackRead
 www.hackread.com
www.hackread.com
Perhaps, the most ironic moments in the cybersecurity world occur when those who promise to protect your online privacy cannot guard their own turf. We’ve seen this happen from time to time with security firms getting hacked themselves. Another similar case has emerged recently when the database of a Hong Kong-based VPN provider called UFO VPN was exposed with more than 20 million users logs.
Discovered by researchers from Comparitech on July 1st, 2020; the exposure occurred due to the database hosted on an Elasticsearch cluster being left without any password.
Worth 894 GB, the data allegedly included plaintext passwords, IP addresses, timestamps of user connections, session tokens, information of the device, and OS being used along with geographical information in the form of tags.
The implications of this are pretty dangerous in that not only user accounts are at risk of being taken over by malicious actors but users can also be tracked online. Furthermore, using the session tokens, any encrypted data that someone gains access to could also be decrypted rendering the entire concept of encryption useless in this scenario.
This is actually a second article as a follow-up to another VPN provider, PureVPN, who claimed to not keep logs, yet provided them to the FBI:
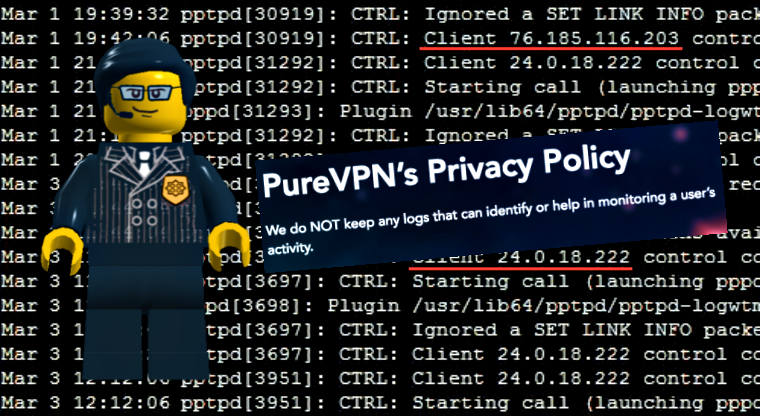
PureVPN Aided FBI to Track CyberStalker by Providing His Logs
On Friday a New Town, Massachusetts based man called Ryan Lin was arrested for cyberstalking after his VPN logs were provided by PureVPN. Lin was accused of
 www.hackread.com
www.hackread.com